
France Titres Bleeds 11.7M Records to One Teenager
Same vendor RFP checklist, but the procurement bar for any provider handling citizen identity data just moved a notch above where most municipal contracts sit.
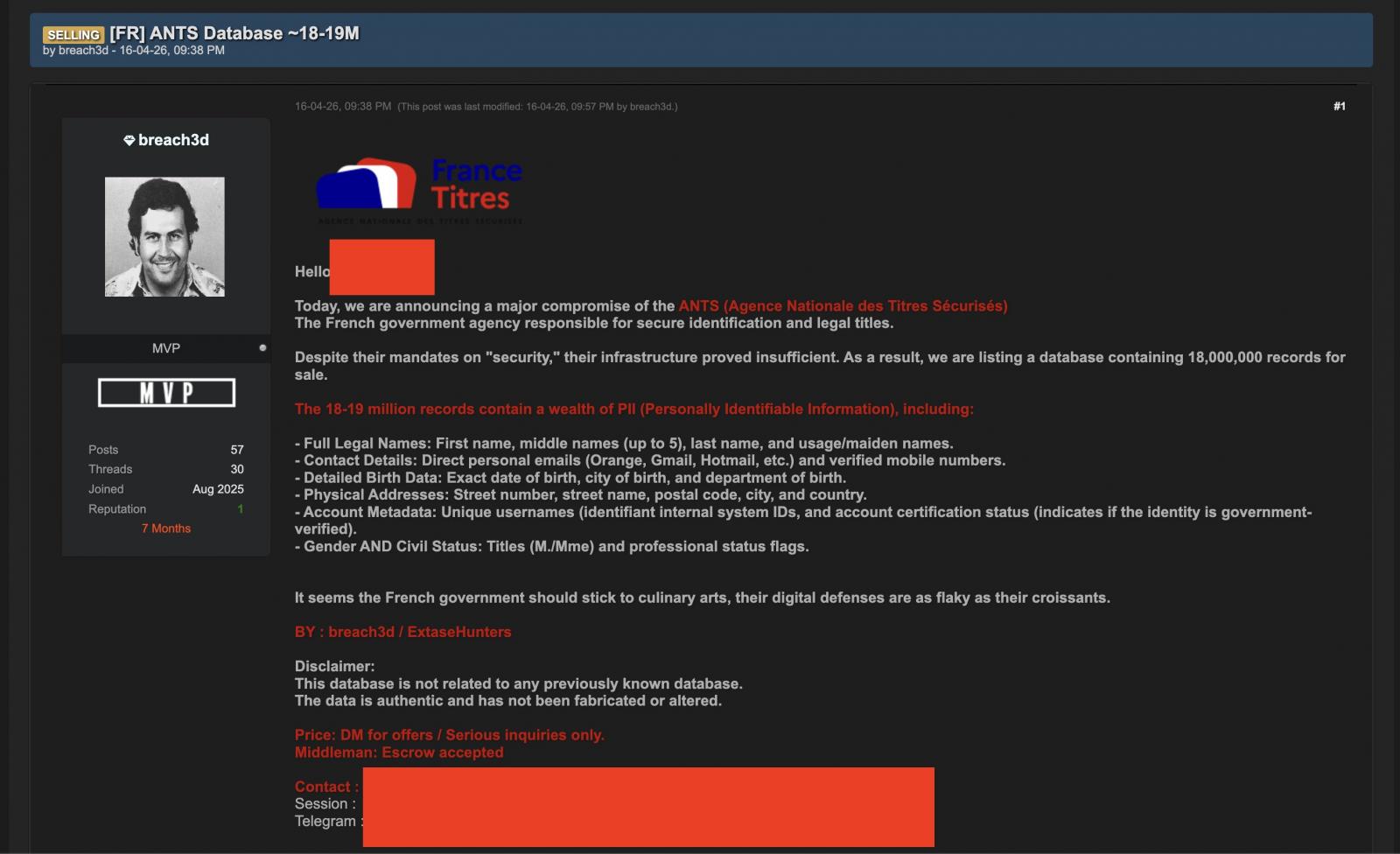
the suspected 15-year-old used the moniker breach3d to offer for sale between 12 and 18 million records stolen in the ANTS data breach
- A 15-year-old, commodity tooling, 11.7M citizen records gone. The attacker-cost floor just dropped through the basement, and vendor attestations don't bound it.
- ANTS detected April 13, notified authorities April 16. Three days. Benchmark your own municipal runbook against that arc, because regulators will.
- EUR 300,000 fine ceiling for the suspect. ANTS's actual remediation cost is uncapped. Read your vendor indemnity clause again before the next renewal.
- Watch UK council and German Land RFPs in Q3 2026. Vendor-security attestation language is about to tighten across civic identity-system procurement.
The public-sector identity-platform category is bifurcating along security posture, and this week's France Titres incident lands cleanly on the buyer-beware side of the line. A 15-year-old, working from a forum alias, walked out with 11.7 million citizen records from ANTS, the French agency that issues and manages administrative documents. The scale isn't novel. The actor profile is. When commodity tooling and a teenage operator can crack a state-run identity registry, the unit economics of vendor diligence in public-sector procurement have to reset, and the comparable deals trade at terms the next RFP cycle will not honour.
The Deployment
On April 13, ANTS detected suspicious activity on its systems. The agency notified authorities three days later, on April 16, according to the Paris Prosecutor's Office. By April 20, ANTS had publicly disclosed that a threat actor had accessed individual and professional accounts on the ants.gouv.fr portal. The exposed data types: full names, email addresses, dates of birth, postal addresses, and phone numbers.
The seller's first claim, posted on a cybercriminal forum under the alias "breach3d," put the dump at up to 19 million records. The agency's revised count: 11.7 million accounts. ANTS added the qualifier that the stolen data could not be used for unauthorised access, meaning authentication material and session credentials were not part of what walked.
The Paris Prosecutor's Office now says the operator behind "breach3d" is a 15-year-old, detained on suspicion of selling the data. The minor faces charges for unauthorised access, persistence, and data exfiltration from a state-run automated personal data processing system, plus possession of software that enables those offenses. Maximum sentence under French law: seven years and a EUR 300,000 fine. A judge is overseeing the case. Prosecutors are seeking formal charges and have requested judicial supervision pending the investigating judge's decision.
Why It Matters
Three structural reads worth the operator-reader's time.
The first is the attacker-economics one. The category baseline for state-grade breaches has historically been nation-state APT actors, bespoke tooling, multi-year persistence, geopolitical motive. France Titres breaks that frame. The actor is an individual minor. The tooling, by the prosecutor's own framing, falls under generic "possession of software that enables the offenses" rather than something custom. The motive is straightforward commercial: sell on a forum. That's the whole stack of a state-registry-class breach operating at the cost structure of a teenage side project. If you're a procurement officer in Munich, Birmingham, or Toronto reading this, the comparable that should anchor your threat-model conversation isn't TalkTalk 2015 or SolarWinds 2020. It's that the floor on attacker capability has dropped, and your vendor's pen-test attestation from Q3 last year does not bound this risk surface.
The second is the vendor-stack one. ANTS runs a portal that handles citizen identity. The same architectural shape, central agency plus citizen-facing portal plus third-party identity vendors plus downstream integrators, applies to roughly every G2C system across the EU and most of the UK. Buyers in this category have absorbed two cost shocks already: AI-tooling line items showing up in vendor contracts, and post-NIS2 compliance overhead for anything designated critical infrastructure. The next shock is one nobody priced. The breach-disclosure cadence is collapsing from "rare event" to "regular event," which forces a re-pricing of cyber insurance premiums, indemnity caps, and the bonded-vendor list. Comparable contracts in this space have traded at vendor-friendly indemnity terms for the better part of a decade. Renewals are about to move the wrong way for vendors.
The third is the public-disclosure one. ANTS detected April 13, notified authorities April 16, disclosed publicly April 20. That's a seven-day arc from detection to public statement, which sits in the right ballpark for what NIS2 and GDPR jointly demand. Other agencies should be benchmarking their own runbooks against that arc. If your detect-to-notify window is measured in weeks rather than days, the structural bear case isn't whether you'll be breached. It's whether the gap between breach and disclosure becomes the regulatory finding that ends your procurement officer's career.
What Other Businesses Can Learn
For SMBs, municipalities, and mid-market firms watching the France Titres arc from outside France, the operator takeaways are concrete and uncomfortable.
First, read your vendor's incident-response SLA in the actual contract, not the marketing PDF. The detect-to-notify clock at ANTS ran in days, which is plausibly the fastest window the regulatory stack allows. Most municipal contracts I have reviewed specify "reasonable promptness" or "within forty-eight business hours of confirmed compromise," language that in practice allows weeks. Push for hard hours, push for an external-disclosure trigger that does not require vendor confirmation. The vendor's interest in delaying disclosure does not align with yours.
Second, stop assuming the attacker profile bounds the threat model. A 15-year-old cracking a state agency reframes the procurement diligence question. The right question for your CISO or IT lead is no longer "is our vendor protecting us against APT-class actors." It is "is our vendor protecting us against any actor with thirty hours, commodity tooling, and a forum login." Those are categorically different thresholds, and most vendor attestations only certify against the first.
Third, price the indemnity gap. The 15-year-old in this case faces a EUR 300,000 fine ceiling. ANTS's actual remediation cost, including incident response, notifications to 11.7 million citizens, regulatory exposure, and brand recovery, is functionally uncapped. If your contract caps vendor liability at a fraction of plausible remediation cost, that gap is now your line item, not the vendor's.
Fourth, assume your data is in the next dump. The records France Titres lost were the boring kind: names, dates of birth, addresses, phones. That matters because it's enough material for downstream identity fraud against the named individuals, regardless of whether ANTS itself lost session credentials. Some fraction of your customer base sits in the 11.7 million already, or in a different agency's next disclosure. Pre-position: tighten KYC checks on accounts with French residency claims this quarter, flag DOB-and-address combinations against leaked-set heuristics, budget the customer-comms cost in advance rather than scrambling.
When commodity tooling and a teenage operator can crack a state-run identity registry, the unit economics of vendor diligence in public-sector procurement have to reset.

Looking Ahead
Across the next twelve to eighteen months, expect at least three more EU public-sector identity-system breaches in the same shape: central registry, citizen-facing portal, individual or small-team actor, commodity tooling. Watch UK Cabinet Office procurement guidance and the German Bundesamt für Sicherheit in der Informationstechnik in particular. Both have been quietly tightening the vendor-attestation frame for civic identity systems, and an ANTS-class incident is the kind of confirmation that pushes draft guidance into mandatory text. The named comparable to watch most closely on the buyer side: any UK county council mid-RFP for a citizen-services portal right now. The clauses that close in Q3 2026 will read very differently from the ones that closed in Q3 2025.
Sources
- BleepingComputer, 15-year-old detained over French govt agency data breach, accessed 2026-05-03
More from the same beat.
Anthropic Plants Sydney Flag, Bleeds Snowflake for ANZ Talent
Same MOU template that ran in DC, London, Tokyo — but the Canberra version comes wrapped in a data-center pipeline and a research-grant moat that locks the next decade of ANZ AI buyers.
- The MOU is the wrapper. The AUD$3M in Claude credits at ANU, Garvan, MCRI and Curtin is the actual lock-in play.
Behind Anthropic's Canberra MOU, OpenAI's APAC Gap Loomed
AUD$3M in research credits reads like ribbon-cutting, but Anthropic just locked its fourth sovereign safety-institute pact while OpenAI sits at zero.
- Four safety-institute pacts now (US, UK, Japan, AU); OpenAI has zero. That's a regulatory moat hardening into a procurement floor.
UT Austin Guts Hospital Plans, Ships AI-First Medical Center
The $2.5B build looks like a hospital, but the ground-up design puts data and AI in the foundation
- The $750M gift locks in AI infrastructure before the first blueprint is finalized, a lesson for any operator building a new facility.